Is there anyway one can edit an already posted WhatsApp update?....is it officially there?Think about it WhatsApp
An experienced CYBER SECURITY ANALYST dealing in transborder crimes on phones,computers,threat intelligence, bug hunting,.... White hat hacking and Repairing phones and reviewer of new technology gadgets
Sunday, September 29, 2019
The dangers of using some VPNs ..The quest to know whether the gorvenment of Uganda spying on opposition chiefs...PART ONe!
Some couple of weeks ago,one politician was complaining of the gorvenment spying on him using Chinese technology gadgets,and all of you know that it was even written in the news paper in America.To me as a cyber security enthusiast,I had to laugh!!! The biggest issue with most of us is that we don't understand the term spying and we knew what is really behind our phones and where they come from then we must know who spying on us.First of all,the Socs of these phones we use are made from foreign countries and some of these gorvenments pattern or sponsor some these projects to come up with Socs or the mobile operating systems.Am sure most of you do use Android Is and it is a fact that CIA ,the USA's spy masters are behind it's commencement and if you are using Android it is just very easy for CIA,FBI,NSA to get any information from and about you.Since the writting of that story the Uganda is using Chinese gadgets and technology to spy on opposition,I have been trying to write a more simple document so that everyone will understand the privacy leakages we are subjective to if we continue using these tech gadgets.And another thing people should understand is that military intelligence is meant to extract information majorly to avoid incidences that may harm the citzens but some individuals want to make it look a devil to the society, actually citzens must work and help them to get such information.
Let me get to these VPNs,at the bringing of the OTT many Ugandans rushed to the use of VPNs and most of them are not aware that they are a security threat to their privacy and general communication.I want every one to read this and take care especially you politicians, business men especially in crypto currency,mobile money,mobile banking etc...!! I was totally shocked when I saw some of you in excitement when you saw a photo of his excellence Yoweri kaguta Museveni using an small old Nokia phone,am sure he read the dangers of over hanging on these smart phones!!!!
What you must know about these VPNs...
The reason people have Virtual private networks (VPNs) is that they protect our online privacy, however, privacy is essentially non-existent if you live in a place where the government is allowed to track your online activities. This is why you need to get a good VPN, the goal is to make sure that you don’t have to worry about third-parties keeping an eye on you. However, while using a VPN, it is important to know if it is in a 14 Eyes country. – Now, that being said, you are probably asking what is a 14 Eyes country.
Before you decide to use a VPN, it is important to have a good amount of background information on the VPN company. In terms of the 14 Eyes countries, they all have entered into the UKUSA Agreement which basically allows countries to share information about international communications between two parties. This is obviously something that would bother VPN users because why should anyone be allowed to access your online activities especially when it does not involve anything illegal such as terrorism or explicit content involving children or animals?
How is the UKUSA Agreement Utilized?
In the United States, it is “illegal” for the government to spy on its citizens. There have to be warrants and lots of other legal proceedings done for the government can surveil its citizens. The United Kingdom, for example, doesn’t have any of the same limitations that the United States has on surveillance of the same American citizen. This could allow the United States under the UKUSA Agreement to give a nudge to UK authorities to look at different folks and see exactly what they are up to.
Naturally, there are certain rights that folks have in different countries that protect their privacy, but in the world of online communications, the legal rulings in these areas are, at best murky. Because there is an evolving legal precedent, it’s difficult for users to know exactly where their rights to privacy in online communications and visits begin and end. That’s why many turn to VPNs since a reliable VPN doesn’t track what you do online.
What are the 14 Eyes Countries?
14 Eyes refer to the countries who have signed the UKUSA Agreement. Obviously, the UK and the USA are part of the 14 countries. The other twelve are:
Italy
Canada,
Australia
Denmark
France
Netherlands
Norway
Germany
Belgium
Sweden
Spain
New Zealand
Additionally, other countries that are believed to be part of the 14 Eyes but not officially are Israel and Japan. After the Snowden leak, it was confirmed that Singapore and South Korea are also taking part in the agreement.
Many countries – especially the United States – can get your internet history and worse yet, they can do so without notifying you. The VPN that is located in a 14 Eyes country is subject to laws that essentially allow the legal system to compel the private entity (a VPN) to surrender information about a user’s web habits.
Furthermore, VPNs in these countries are forced to keep logs of exactly what someone browses and what they do on the Internet. Therefore, if you are going to use a VPN, it is extremely wise to get a VPN that is not based in any of the 14 eyes countries and be wary of any VPN based in Singapore, South Korea, Israel, and Japan.
How do I Find Out Where a VPN is Located?
It is actually not too difficult to find out which VPNs are not based within the 14 Eyes countries. The easiest way to find this out is to do a Google Search, but when you look at a VPN’s landing page you will notice the address at the bottom will probably tell you where it is based. If you are still not sure, look at the billing information.
Some countries where you may find great VPNs in are Hong Kong, Taiwan, and several Eastern European nations that are part of the EU and NATO. These countries allow you to have the technical savvy of one of the 14 Eyes countries while not having to deal with the different issues that plague VPN usage such as a lack of privacy.
Selecting a Good VPN
The key to selecting a good VPN is first understanding the purpose. There are different VPNs for gaming and others that are great for streaming. However, when looking generally at a VPN, the key is having a few really solid features. Understand that you’ll have to pay for a VPN, but what they offer makes it worth it.
The first feature to look for is a large number of servers. This will allow you to select the server closest to you. A close server allows for a better connection, especially in terms of gaming. Another important factor is that the VPN doesn’t track your data. This is why many people trust VPNs, and when you have a VPN from a place that isn’t part of the 14 Eyes nations, then you have a VPN that you can trust.
Another important consideration is the ease of use of a VPN. When you get one that doesn’t make it too complicated to log on and get to work, then you will have no problem using the VPN for all of your purposes.
Conclusion
Unfortunately, such governments that sponsors such tech programmes,software,gadgets,system,etc always try to overreach into what you do in the privacy of your home. While you are working at getting a VPN that’s not based in one of the 14 Eyes countries, be sure that your information is not being tracked by free VPNs since such providers are known for selling browsing data to third-parties.
Nevertheless, VPNs provide great security and protect your privacy very well, so be sure you get a VPN that keeps your information away from overreaching governments.
Saturday, September 21, 2019
Are you aware of your web camera's leakage of your data
Every cybersecurity article you’ll find will include some sort of reminder emphasizing the use of strong passwords, good antivirus software and the related usual. However, there is less care taken to ensure the hardware components of our computers are secure.
In the wake of this, Avishai Efrat, a white hat hacker from Wizcase has found 15,000 webcams globally that can be accessed unauthorizedly with the only pre-requisite being an Internet connection. Many of these webcams can also be tinkered with by malicious users editing their settings which is made easier by the fact that most users do not bother changing the default credentials of such devices.
Some of the manufacturers include:
AXIS net cameras
Cisco Linksys webcam
IP Camera Logo Server
IP WebCam
IQ Invision web camera Mega-Pixel IP Camera,
Mobotix
WebCamXP 5
Yawcam.
These have been found installed both for home and business use in different countries with the following ones being the most popular as reported by Wizcase:
Argentina
Australia
Austria
Brazil
Canada
France
Germany
Italy
Japan
Pakistan
Russia
Spain
Switzerland
UK
USA
Vietnam
While webcams at homes would be expected to mostly have revealed personal sensitive information in developing countries where the trend of remote working is less, this is untrue for economies based particularly in Europe and the Americas where important business data may have also been compromised.
But that’s not where it ends. Potential uses of webcams also extend to places of worship, museums, sports areas and parking lots which could be deemed as an invasion to the privacy of users.
Here, it’s noteworthy that since 2014, a website called “Insecam” has been showing live footages from over 100,000 insecure private security cameras from all over the world. The site claim to be “The world biggest directory of online surveillance security cameras.”
Some of the consequences of these are that indecent footage of people could be used for blackmailing them, IP theft could become easier for unethical businesses who may utilize such feeds, surveillance becomes easier for both government and foreign government agencies, camera loops could be set to coordinate physical attacks and much more – the list is endless to say.
The golden question is, why was such a flaw overlooked by several manufacturers despite the implications? To answer this, we must look at how webcams work. Every time one is installed, users need some remote way in order to access its footage either in real-time or later for play-back. This is important to realize as not all webcams are used for video networking communication and many of them are utilized for security purposes.
The access mechanisms can be divided into two networking protocols, namely port forwarding and peer to peer(P2p). In port forwarding through the use of Universal Plug and Play (UPnP) technology, the camera can be accessed by a port on the external IP address.
If there is no authentication method, anyone who knows the IP address of the device can access the footage and other privileges depending on the manufacturer’s setup. Secondly, in P2P, the device itself communicates with the manufacturer’s servers for administration and other functions without port forwarding leaving no need for port forwarding.However, this can again be insecure if the manufacturer doesn’t take the basic precautions mentioned above. To solve these security issues, Chase from Wiscase offers some insight along the lines of,
“Many devices aren’t put behind firewalls, VPNs, or whitelisted IP access – any of which would deny scanners and arbitrary connections. If these devices have open network services, then they could be exposed. wrote Chase.” “The device’s security posture might depend on different things but a recommended way to set up a secure web camera would be to use a local VPN network, so that any open port would remain within the limits of the encrypted communication of the VPN. The app would connect to the VPN which would then access the port using an internal IP, thus avoiding the open port & call home potential problems and removing accessible ports from your external IP,” Chase concluded.
Furthermore, one can also add other measures such as whitelisting only one’s own device’s MAC addresses, choosing vendors with a focus on security, enabling two-factor authentication and finally using an encrypted connection to access the admin panel.
Finally, If you’re not a technically interested user, checking if your public IP address is compromised through a search engine like Shodan can also help for the immediate time being helping you decide your next course of action.
Every cybersecurity article you’ll find will include some sort of reminder emphasizing the use of strong passwords, good antivirus software and the related usual. However, there is less care taken to ensure the hardware components of our computers are secure.
In the wake of this, Avishai Efrat, a white hat hacker from Wizcase has found 15,000 webcams globally that can be accessed unauthorizedly with the only pre-requisite being an Internet connection. Many of these webcams can also be tinkered with by malicious users editing their settings which is made easier by the fact that most users do not bother changing the default credentials of such devices.
Some of the manufacturers include:
AXIS net cameras
Cisco Linksys webcam
IP Camera Logo Server
IP WebCam
IQ Invision web camera Mega-Pixel IP Camera,
Mobotix
WebCamXP 5
Yawcam.
These have been found installed both for home and business use in different countries with the following ones being the most popular as reported by Wizcase:
Argentina
Australia
Austria
Brazil
Canada
France
Germany
Italy
Japan
Pakistan
Russia
Spain
Switzerland
UK
USA
Vietnam
While webcams at homes would be expected to mostly have revealed personal sensitive information in developing countries where the trend of remote working is less, this is untrue for economies based particularly in Europe and the Americas where important business data may have also been compromised.
But that’s not where it ends. Potential uses of webcams also extend to places of worship, museums, sports areas and parking lots which could be deemed as an invasion to the privacy of users.
Here, it’s noteworthy that since 2014, a website called “Insecam” has been showing live footages from over 100,000 insecure private security cameras from all over the world. The site claim to be “The world biggest directory of online surveillance security cameras.”
Some of the consequences of these are that indecent footage of people could be used for blackmailing them, IP theft could become easier for unethical businesses who may utilize such feeds, surveillance becomes easier for both government and foreign government agencies, camera loops could be set to coordinate physical attacks and much more – the list is endless to say.
The golden question is, why was such a flaw overlooked by several manufacturers despite the implications? To answer this, we must look at how webcams work. Every time one is installed, users need some remote way in order to access its footage either in real-time or later for play-back. This is important to realize as not all webcams are used for video networking communication and many of them are utilized for security purposes.
The access mechanisms can be divided into two networking protocols, namely port forwarding and peer to peer(P2p). In port forwarding through the use of Universal Plug and Play (UPnP) technology, the camera can be accessed by a port on the external IP address.
If there is no authentication method, anyone who knows the IP address of the device can access the footage and other privileges depending on the manufacturer’s setup. Secondly, in P2P, the device itself communicates with the manufacturer’s servers for administration and other functions without port forwarding leaving no need for port forwarding.However, this can again be insecure if the manufacturer doesn’t take the basic precautions mentioned above. To solve these security issues, Chase from Wiscase offers some insight along the lines of,
“Many devices aren’t put behind firewalls, VPNs, or whitelisted IP access – any of which would deny scanners and arbitrary connections. If these devices have open network services, then they could be exposed. wrote Chase.” “The device’s security posture might depend on different things but a recommended way to set up a secure web camera would be to use a local VPN network, so that any open port would remain within the limits of the encrypted communication of the VPN. The app would connect to the VPN which would then access the port using an internal IP, thus avoiding the open port & call home potential problems and removing accessible ports from your external IP,” Chase concluded.
Furthermore, one can also add other measures such as whitelisting only one’s own device’s MAC addresses, choosing vendors with a focus on security, enabling two-factor authentication and finally using an encrypted connection to access the admin panel.
Finally, If you’re not a technically interested user, checking if your public IP address is compromised through a search engine like Shodan can also help for the immediate time being helping you decide your next course of action.
Friday, September 13, 2019
The joker malaware
Another day, another Android malware – This time; The Joker malware is here not to creep you out but steal from you.
While “The Joker” might be your favorite villain fighting the dark knight, a new malware that goes by the name of it may not entertain you.
It has been recently discovered by researcher Aleksejs Kuprins, that The Joker malware infected 24 apps on the Google Play Storewhich had over 472,000 installations.
After successfully being deployed, the malware tricks and scams users by signing them up for premium subscription services all without their knowledge. It does so by using the background component and stealthily clicking on advertisements and other processes intended to reach its final goal.
Finally, since an authorization code would be required usually for confirming payments, it accesses the user’s SMS messages and copies any code needed.
However unlike most malwares, it only targets users in specific countries. This is evident as the apps infected contain mobile country codes from which the sim should belong to for it to receive the payload.
For example, in Denmark, Joker can silently sign the victim up for a 50 DKK/week service (roughly ~6,71 EUR). This strategy works by automating the necessary interaction with the premium offer’s webpage, entering the operator’s offer code, then waiting for a SMS message with a confirmation code and extracting it using regular expressions. Finally, the Joker submits the extracted code to the offer’s webpage, in order to authorize the premium subscription, wrote Kuprins in his blog"
Thursday, September 12, 2019
You can now easily take video download from Facebook, Instagram,YouTube,Twitter....
With the widespread availability of the Internet today, there are still times when it may not be feasibly available. Be it on a flight, during the commute to work or simply put the blame on poor network reach, such situations can arise frequently.
For example, suppose I need to watch a lecture on YouTube but I won’t have access to the Internet on my flight later on in the day. I’ll simply download the lecture up ahead and watch it offline later then. Furthermore, people like journalists, bloggers and videographers can download videos to analyze or edit them according to their needs.
If you can relate, turns out that you could easily download online video and audio files using a new downloading tool from SaveFrom.net to watch them later.
You can do so in 4 simple steps:
- Visit SaveFrom.net by entering the URL in your browser bar.
- Enter the video link from which you want to download in the search bar. You could also alternatively add “ss” before the URL and press enter in the browser bar which will lead you directly to the site. For example, “ssyoutube.com” could be used.
- Choose the video resolution from the dropdown right to the download button, different options are available here depending on your needs. You can also download it in MP3 form by clicking the button to the far right beside it.
- Click on the download button and the video will start downloading.
Tada! It’s that simple and easy-to-use. Such files can also be downloaded from additional resources including Instagram, DailyMotion, Twitter, SoundCloud, and Facebook.
For those of you who prefer in-browser extensions, you can install the tool on Chrome by runningSaveFrom’s script through another extension named MeddleMonkey.
For Android users, they may download a dedicated app for their device while iPhone users will have to use it with the help of another third-party tool as Apple does not allow direct downloading of music and videos.
As with everything, privacy & security-focused users can be relieved that all the videos downloaded are never stored by the tool and remain on the source’s servers. Moreover, upon a scan of the site by Norton, the result displays no safety issues. If you lose the video you downloaded, you can simply re-download it using the aforementioned steps. Seems like a win-win for all!
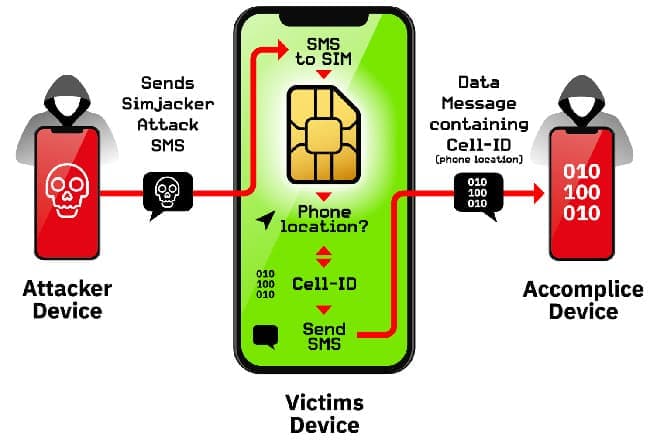
The Sim jacker vulnerability
The Simjacker vulnerability could extend to over 1 billion mobile phone users globally.
As time passes, we’re witnessing more exploits building upon the usage of sim cards including the ever-famous sim swapping method. To add to these, just recently, AdaptiveMobile Security had released details of a previously undiscovered exploit dubbing it as SimJacking. How it apparently works is illustrated very simply with the help of a diagram below, however, there’s more to its intricacies.
Sunday, September 8, 2019
US DOJ to subject Google, Facebook and other to antitrust investigation
company Alphabet has confirmed that it is under investigation by the United States Department of Justice. Specifically, the DOJ suspects Alphabet of antitrust practices, and is demanding all information and documents related to prior antitrust investigations involving the company around the globe. While the DOJ stated that it was just beginning to investigate major tech companies back in July 2019, we now know the department's efforts have kicked into high gear.

Alphabet and Google aren't the only major tech companies under the crosshair right now. Apple, Facebook, and Amazon are all known to be under investigation as well, and we wouldn't be surprised if other platforms like Twitter soon found themselves under scrutiny, too. President Trump has quite the love-hate relationship with Twitter, as he uses it frequently to announce major policy decisions and communicate with the general populous. He has also criticized the platform, however, (along with Google) with accusations of bias.
So, what does all of this mean for you, a consumer? For now, nothing. In the future, however, we're likely to see these bigger tech companies become more reigned-in. In the case of giants like Facebook and Google, who command a massive percentage of any given market as well as corporate entities, we wouldn't be surprised to see their empires divided.

Alphabet and Google aren't the only major tech companies under the crosshair right now. Apple, Facebook, and Amazon are all known to be under investigation as well, and we wouldn't be surprised if other platforms like Twitter soon found themselves under scrutiny, too. President Trump has quite the love-hate relationship with Twitter, as he uses it frequently to announce major policy decisions and communicate with the general populous. He has also criticized the platform, however, (along with Google) with accusations of bias.
So, what does all of this mean for you, a consumer? For now, nothing. In the future, however, we're likely to see these bigger tech companies become more reigned-in. In the case of giants like Facebook and Google, who command a massive percentage of any given market as well as corporate entities, we wouldn't be surprised to see their empires divided.
Talk of breaking up companies like Facebook and Google has been rumbling for years now in political spheres. However, we'd be more surprised to see any damage done to their fundamental services; i.e. Google's Search/AdSense and Facebook's main social networking platforms. Fortunately for web users and advertisers at large, though, that scenario seems quite unlikely.
Saturday, September 7, 2019
As I warned markzuckerberg few months ago,then you can see this privacy disaster on Facebook!!! Next has to be WhatsApp...
Some few days ag
o another privacy disaster hits Facebook users.But mark Zuckeberg and his team would not have read such news with surprise because I remember few months ago I wrote about the database uncertainties and irregularities especially in the login credentials.I have read mant tweets about this and seemingly many this it is a problem prone to the western hemisphere,am telling you that"africa" is also under this privacy threat!!It should be noted carefully that even whatsApp is with privacy issues,under some research on security of social media,I in June this year discovered that the VPNs used mainly in African can make many fall prey to privacy leakages of which leakages are Paramount to the users security in terms of gps location ,phone book,calls and sms ...etc..i i wi write about this later in my final analysis by the end of September.
To add insult to the already enraged privacy advocates, Facebook has yet again disappointed its user base. It has been revealed that 419 million phone numbers belonging to Facebook users have been exposed due to a breach in an online unsecured database.
The database contained 133 million records from the US, 18 million in the UK and 50 million in Vietnam. However, a Facebook spokeswoman has added that in actuality the data of 210 million users was revealed since the unsecured database contained duplication.
About more than a year ago, if you entered a phone number into Facebook’s search bar, it would reveal the account connected to that number. Although Facebook has abandoned this practice, it is believed that the phone numbers were scraped before it did so.
Unsecured database leaked phone numbers of 419 million Facebook users
Screenshot of the leaked database
However, according to GDI Foundation’s security researcher Victor Gevers tweeted that “Although Facebook had disabled the API that shares users mobile phone & address details back in 2011, this data leak with scraped Facebook details was deployed recently in August 2019 on the latest version (4.0.12) of MongoDB. There is also a mail server running on that server.”
Although Facebook had disabled the API that shares users mobile phone & address details back in 2011, this data leak with scraped Facebook details was deployed recently in August 2019 on the latest version (4.0.12) of MongoDB. There is also a mail server running on that server 🤔 https://twitter.com/zackwhittaker/status/1169327242528219136 …
There were several databases on the exposed server containing 419 million records — including 133 million on U.S.-based Facebook users and 18 million on U.K. users.
Nevertheless, the breach is still alarming for a number of reasons. Firstly, phone numbers are a goldmine for hackers who would definitely enjoy sending loads of marketing messages and calls to these users.
Secondly, they could be used to aid in sim swapping for users who have been using their phone numbers as a part of two-factor authentication. How serious can this be? Well, last week, Jack Dorsey’s Twitter account was compromised just due to such a technique despite him being the CEO so this leaves a layman much more vulnerable.
Moreover, the phone numbers were linked to Facebook accounts identifiable by a unique public ID assigned by the platform and that could be used to discern someone’s username.
“TechCrunch verified a number of records in theunsecured database by matching a known Facebook user’s phone number against their listed Facebook ID. We also checked other records by matching phone numbers against Facebook’s own password reset feature, which can be used to partially reveal a user’s phone number linked to their account,” reported the site.the unsecured database has been taken down with Facebook investigating in the meanwhile. We do not know if the affected users would be compensated in any way or even be informed. This leaves us with a simple yet profound lesson of not relying on companies no matter how big they may seem, there will always be human errors after all.
o another privacy disaster hits Facebook users.But mark Zuckeberg and his team would not have read such news with surprise because I remember few months ago I wrote about the database uncertainties and irregularities especially in the login credentials.I have read mant tweets about this and seemingly many this it is a problem prone to the western hemisphere,am telling you that"africa" is also under this privacy threat!!It should be noted carefully that even whatsApp is with privacy issues,under some research on security of social media,I in June this year discovered that the VPNs used mainly in African can make many fall prey to privacy leakages of which leakages are Paramount to the users security in terms of gps location ,phone book,calls and sms ...etc..i i wi write about this later in my final analysis by the end of September.
To add insult to the already enraged privacy advocates, Facebook has yet again disappointed its user base. It has been revealed that 419 million phone numbers belonging to Facebook users have been exposed due to a breach in an online unsecured database.
The database contained 133 million records from the US, 18 million in the UK and 50 million in Vietnam. However, a Facebook spokeswoman has added that in actuality the data of 210 million users was revealed since the unsecured database contained duplication.
About more than a year ago, if you entered a phone number into Facebook’s search bar, it would reveal the account connected to that number. Although Facebook has abandoned this practice, it is believed that the phone numbers were scraped before it did so.
Unsecured database leaked phone numbers of 419 million Facebook users
Screenshot of the leaked database
However, according to GDI Foundation’s security researcher Victor Gevers tweeted that “Although Facebook had disabled the API that shares users mobile phone & address details back in 2011, this data leak with scraped Facebook details was deployed recently in August 2019 on the latest version (4.0.12) of MongoDB. There is also a mail server running on that server.”
Although Facebook had disabled the API that shares users mobile phone & address details back in 2011, this data leak with scraped Facebook details was deployed recently in August 2019 on the latest version (4.0.12) of MongoDB. There is also a mail server running on that server 🤔 https://twitter.com/zackwhittaker/status/1169327242528219136 …
There were several databases on the exposed server containing 419 million records — including 133 million on U.S.-based Facebook users and 18 million on U.K. users.
Nevertheless, the breach is still alarming for a number of reasons. Firstly, phone numbers are a goldmine for hackers who would definitely enjoy sending loads of marketing messages and calls to these users.
Secondly, they could be used to aid in sim swapping for users who have been using their phone numbers as a part of two-factor authentication. How serious can this be? Well, last week, Jack Dorsey’s Twitter account was compromised just due to such a technique despite him being the CEO so this leaves a layman much more vulnerable.
Moreover, the phone numbers were linked to Facebook accounts identifiable by a unique public ID assigned by the platform and that could be used to discern someone’s username.
“TechCrunch verified a number of records in theunsecured database by matching a known Facebook user’s phone number against their listed Facebook ID. We also checked other records by matching phone numbers against Facebook’s own password reset feature, which can be used to partially reveal a user’s phone number linked to their account,” reported the site.the unsecured database has been taken down with Facebook investigating in the meanwhile. We do not know if the affected users would be compensated in any way or even be informed. This leaves us with a simple yet profound lesson of not relying on companies no matter how big they may seem, there will always be human errors after all.
Subscribe to:
Comments (Atom)
-
A new way for cybercriminals to create fake social media profiles and carry identity scams using Artificial Intelligence powered tool? A ...
-
The Democratic Republic of Congo (DRC) has long been a battleground for complex conflicts, driven by historical betrayals, foreign interfe...
-
- When writing an Android exploit, breaking out of the application sandbox is often a key step. There are a wide range of remote attacks th...