In the past, Apple has repeatedly refused to unlock the iPhone for the FBI pleasing its fan base with the notion that it indeed has no secret backdoor to your smartphone. Yet, this sadly did not mean that the iPhone was unhackable.
In fact, there have been numerous instances including strange cases such as when a teenager hacked Apple twice. No massive black hat teams sitting behind a plethora of big screens, literally a teenager.
Now, another incident is on the rise with it being reported that the FBI can unlock all iPhones using Graykey – a product of Grayshift, an Atlanta based company. Moreover, this is not the first time that the tool has been in the headlines for helping unlock any iPhone using brute force techniques.
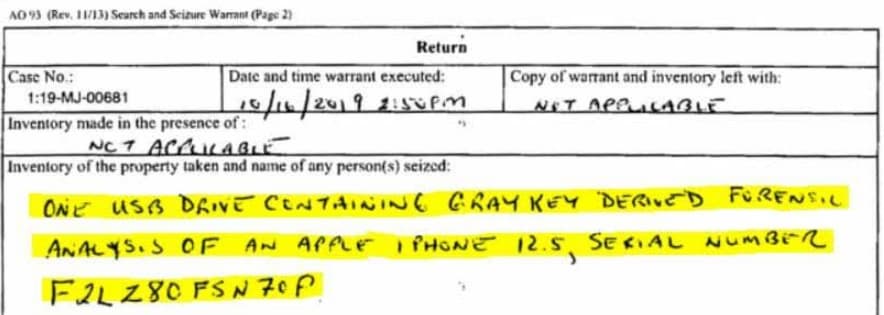
As reported by Thomas Brewster from Forbes, a search warrant of a United States District Court for Ohio dated October 16 of last year confirms the use of such a device to obtain forensic data:
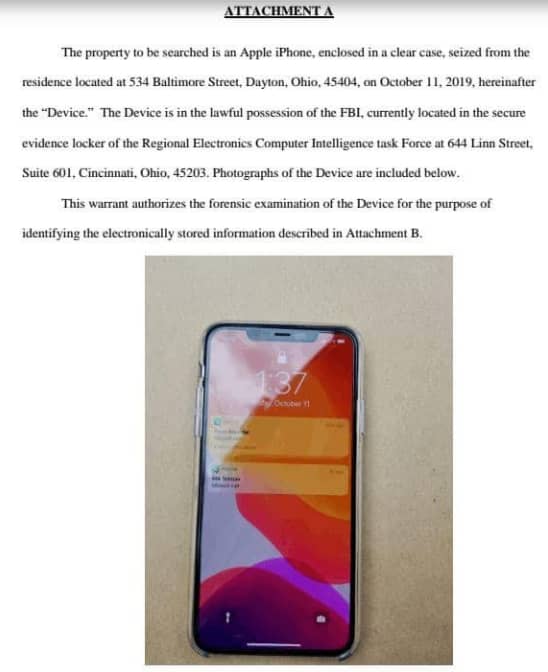
The iPhone in question was an 11 Pro Max belonging to Baras Ali Koch, a man alleged to have helped his brother escape the U.S following an arrest order using Baras’s passport. An alarming thing emerging from this is that it was expected that iOS 13 would finally guard against such attacks but alas, it doesn’t seem to get any better.
What if the iPhone was already unlocked? To debunk this, Thomas reports that Forbes themselves confirmed from Koch’s lawyer, Ameer Mabjish, that the device was locked. Adding further, he stated that
“Koch had not given it to them nor did they force the defendant to use his face to unlock the phone via Face ID, as far as the lawyer was aware.”
We also analyzed an application of a search warrant as shown below which clearly shows the suspect’s iPhone locked in an attachment within.
It is important to note though that the FBI is not the only government agency to possess such tech. Previously, the Immigration Customs and Enforcement Authority (ICE) has made hefty purchases in the past amounting to over $1.2 million.
This though poses another question, if the FBI can hack any iPhone in this way, why ask Apple for help? The reason is that Apple has been stepping up its efforts on the side such as introducing a USB restricted mode with iOS 12 which prevents tools like Graykey from working. Moreover, the tool would not be a success in all cases as certain measures can be taken to resist i
To start with, since a brute force technique is being used, you can start using longer digit passcodes instead of the more often used 4 digit ones. To put this in perspective, Caleb from PIA explains by stating that:
“It takes Graykey an average of 6.5 minutes to crack a four-digit passcode. For a six-digit passcode, the time needed is 11.1 hours on average. A 10 digit passcode, the maximum allowed, requires Graykey an average of 4629 days to average.”
However, we’re still wondering why Apple has failed to implement measures that resist tools like Graykey under normal conditions. Is it something intentional while maintaining a public stand to appease both governments and its users or is it a coincidence? What do you think? Let us know in the comment section.
Nevertheless, this is not the first time when Feds have unlocked an iPhone device without Apple’s help. In 2016, the FBI used Israel based firm CellebriteCellebrite to unlock the iPhone 5C device of San Bernardino suspected shooter